
Cybersecurity Basics for Small Businesses (Part 2)
In our first Cybersecurity Basics blog, we discussed the danger small businesses face when being targeted by cyber-criminals. A 2018 report indicated that “58% of cyber attack victims were small businesses,“ defined as organisations with less than 250 employees. And while we previously focused on the usage of Multi-Factor Authentication, how to share login details, how to spot a phishing email, and where you can acquire more help on these issues, today we’re tackling further comprehensive tips and skills your business can learn in order to stay well ahead of the game.
1. UTILISING SAFE LINKS FOR EMAIL
One of the most common dangers small businesses face these days is malicious URL links sent to them over email. Links that, once clicked on, can lead unsuspecting recipients straight into the trap of a cyber-criminal.
While filters such as anti-spam and anti-malware automatically scan any emails sent to you, dangerous links can often dodge this precaution. How do they do that? Well, certain tools (e.g. Bitly) actually allow link owners to change where a particular URL leads to. This means cyber-criminals can establish a URL that leads to a safe and inconspicuous website. That way, when an email with that link is sent to you and scanned for anything dangerous, nothing is found.
This is where the hackers get a step ahead.
Once that link is in your email, sitting in your inbox, the criminals can then change the website that that URL leads to, leaving you wide open for attack when clicking on said link. See it as a Trojan horse of sorts.
However, thankfully, there is a counter to these hacker tricks, and that is Safe Links! When using this tool, upon clicking on any URL link in your email, Safe Links will instantly scan the site itself to ensure your security. And the best part is, you’ll barely even notice it’s happening! If the site is deemed safe, you’ll be let in with ease. If the site is found to be malicious, however, a notification page will open for you, letting you know exactly what’s wrong.
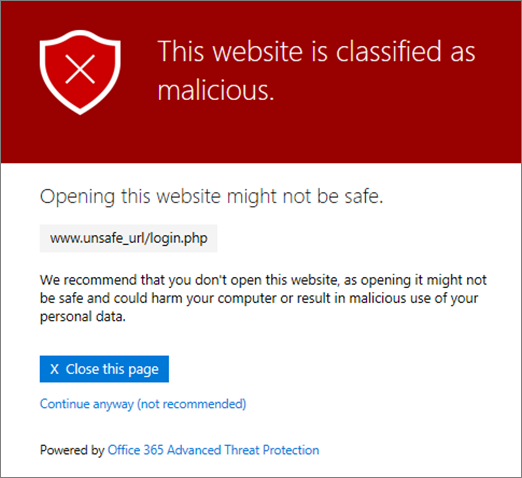
(Above: A Safe Links malicious warning page)
The extra layer of protection this tool gives you is crucial in securing your business against the most common form of cyberattacks today, relieving the worry of ever having to open another threatening and dangerous link again. If you are eager to up the safety of your business, the feature is included with our own AxiomCLOUD service.
2. IDENTIFYING FAKE EMAIL SENDERS
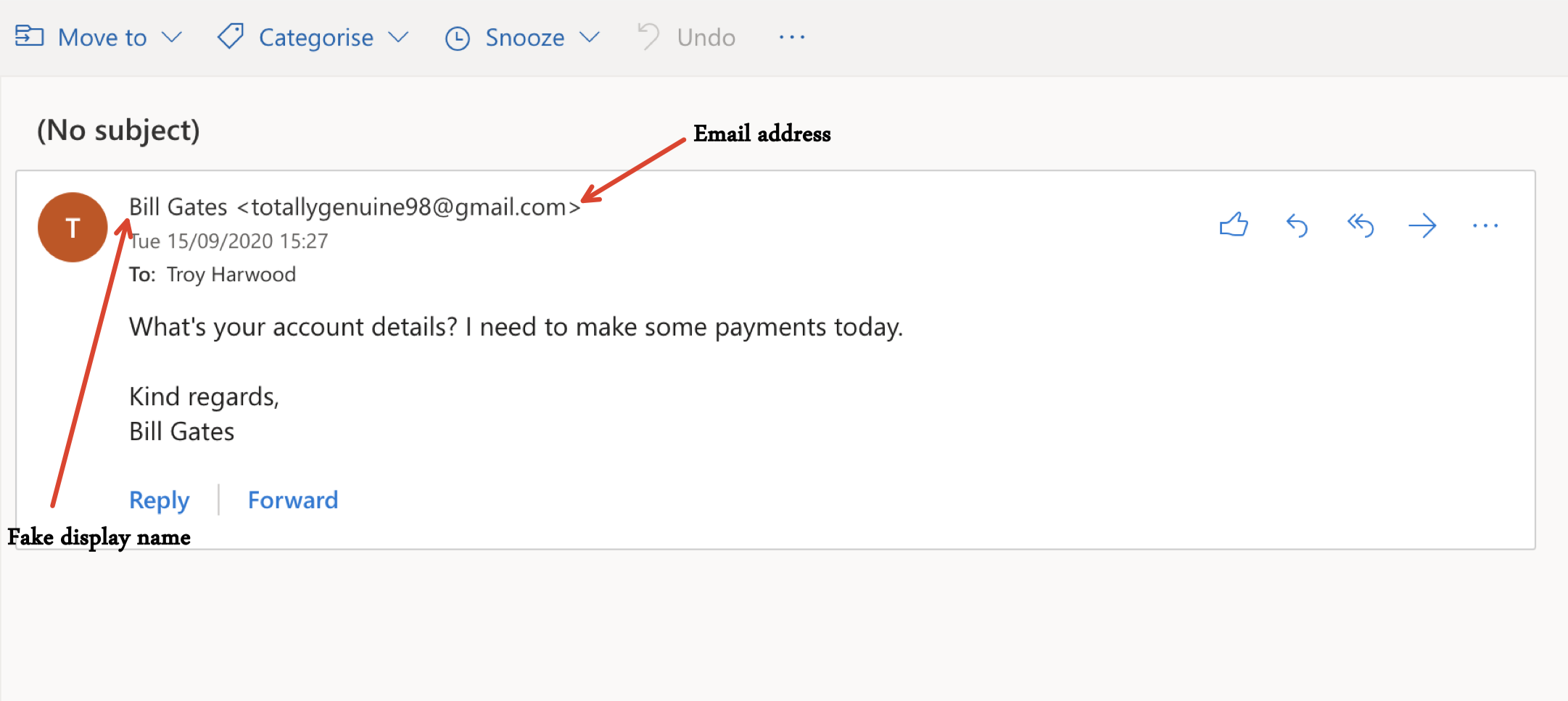
One of the more recent popular scamming techniques cybercriminals use is a simple yet effective one, changing their email display name. How this works relies on how email services usually show a display name of the contact you are emailing with, rather than their literal email address. The catch here is that this display name is often easily editable on services like Gmail and Microsoft Outlook. So, scammers can change their display name to someone you know or are familiar with, tricking you into thinking you’re conversing with a known contact. With the ease and openness of social media these days it’s dangerously simple for criminals to find out who the company you work for, the people you work with, and who your friends and family are, and thus, use those identities to lure in unsuspecting victims.
Fortunately, however, this is a relatively easy trap to avoid. While the display name can be changed, the actual email address itself can’t be. So, all you have to do is check the email address of the sender. If it is from a criminal, the address will often not match up with the name on their display.
However simple the solution may be, many still fall for these devious tricks, so it never hurts to learn more. For more information on how to spot the trappings of these types of phishing emails, take a look at our How to Identify a Scam Email blog. Another helpful way to learn more about the common signs of scam emails is to review resources published by the Australian Signals Directorate specifically for SMBs.
3. USING A PASSWORD MANAGER
In our previous blog we discussed the problem with sharing passwords amongst your staff, which makes whatever you’re trying to keep secure even more vulnerable. This is heightened by the lack of effort many people put into changing their passwords regularly, as well as people often reusing the same password multiple times. If you happen to be someone reusing the same password across numerous sites and accounts, once a cybercriminal gets their hands on that one password, it’s all too easy for them to use your username, email and password combination on as many websites as possible. Everything you have used that password for will be in danger. To see if your email has already been compromised, check out https://haveibeenpwned.com/ in order to begin securing yourself more.
Even people having basic, easy-to-guess passwords is a frequent issue these days. In a study done by the UK’s National Cyber Security Centre, the password ‘123456’ was found to be the most commonly used password, with “23.2 million accounts using the easy-to-crack code“.
The source of this issue is of course the worry of creating a password too complex to remember. However, thankfully there is a solution to our forgetfulness – LastPass! This password manager tool can be easily downloaded onto your web browser and mobile devices, and will ensure that you no longer have to remember another password again. The system allows you to create a vault of passwords for however many sites and logins you need, it will generate randomised and complex passwords, auto–fill your logins when you sign in somewhere, sync your passwords between multiple devices, and much more.

Utilising solid encryption algorithms, Multi-Factor Authentication, and localising your data so that even LastPass don’t have access to your details all makes LastPass a must-have tool when looking to secure your online and digital data.
SECURING THE NEXT STEP
If you’re now adopting Safe Links, identifying fake emails, or using LastPass – you are one step closer to keeping your business more secure than ever! Axiom IT proudly offers help and training to our clients regarding all of these areas, keeping them prepared and confident to handle the security of their business’ data. For more information, call us at 1300 991 992 or email [email protected]. You can also visit our contact page for more information.